iSecurity GUI Release News
Version 5.1.11 (March 2024)
Audit
New Features
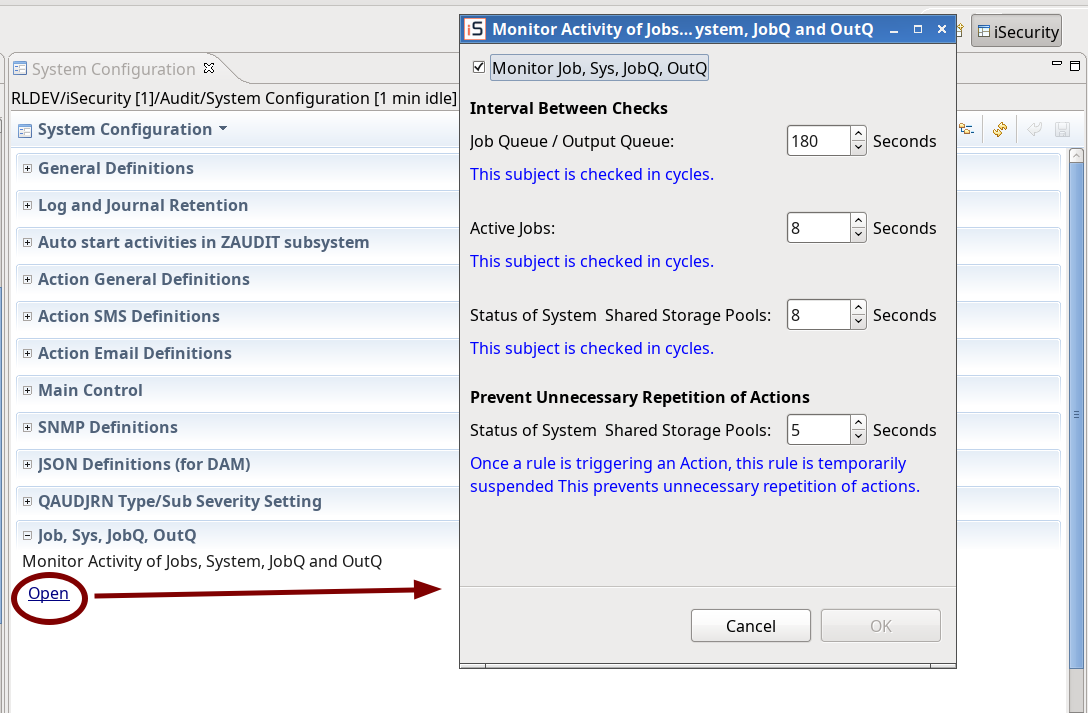
- System Configurations: Added Monitor Activity of Jobs, System, JobQ and OutQ
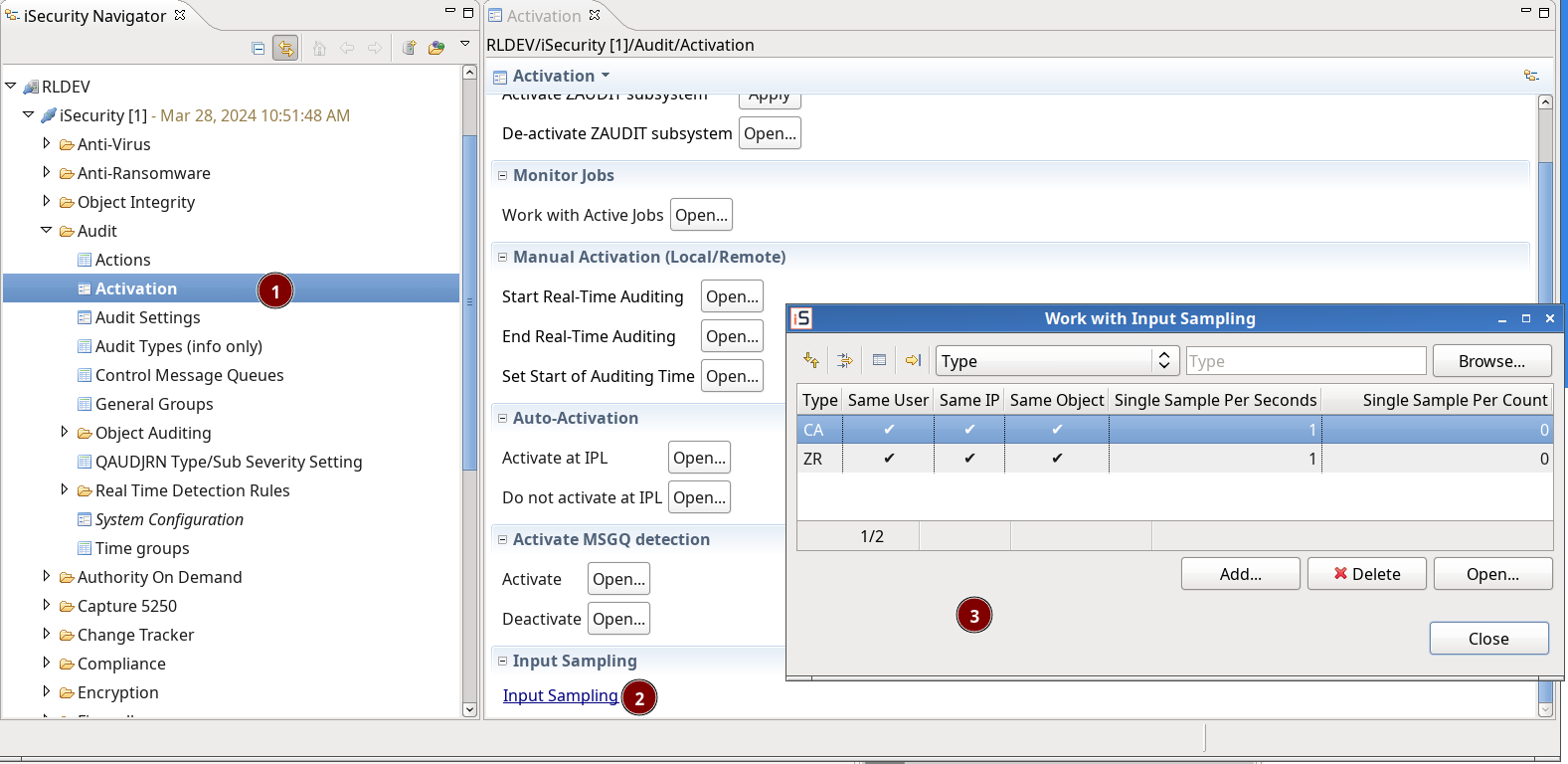
- Input sampling: Added a link for the dialog
Firewall
Enhancements
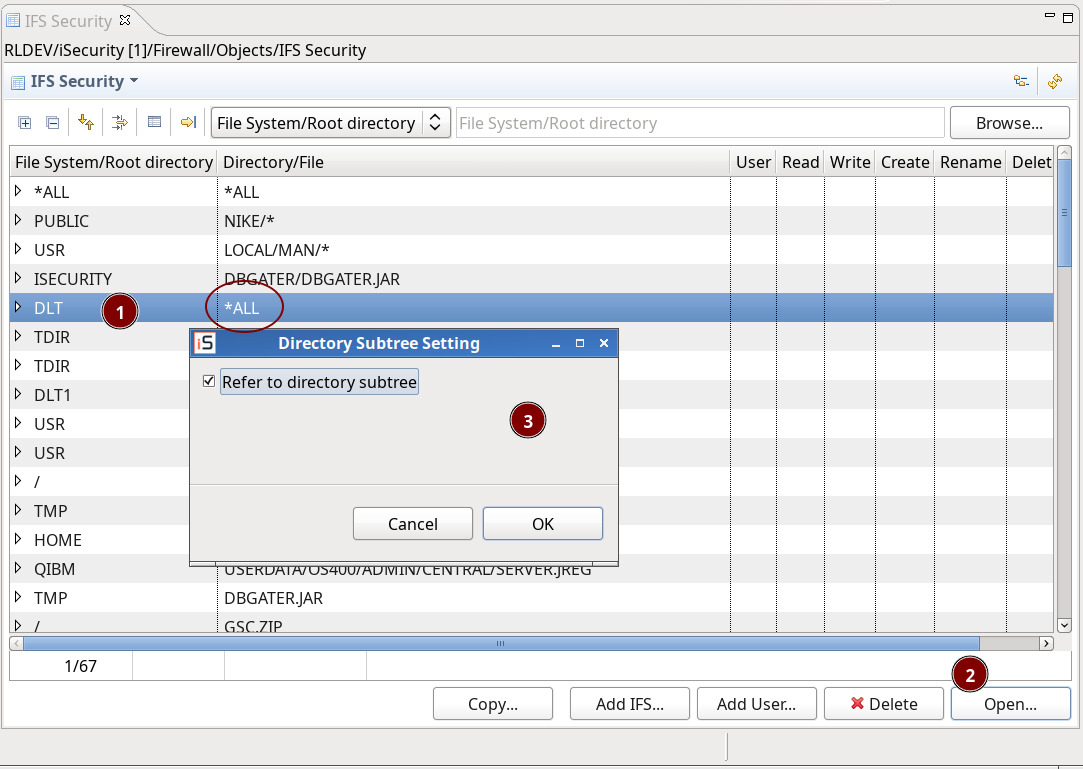
- IFS Security in Firewall 19.03: Allow Open for directories that are *ALL
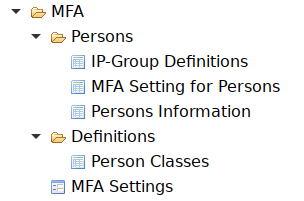
MFA
New Features
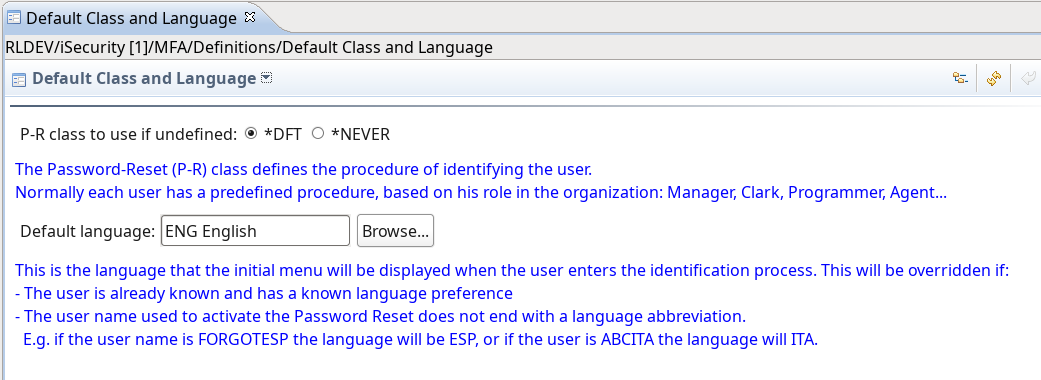
- Default Class and Language.
Enhancements
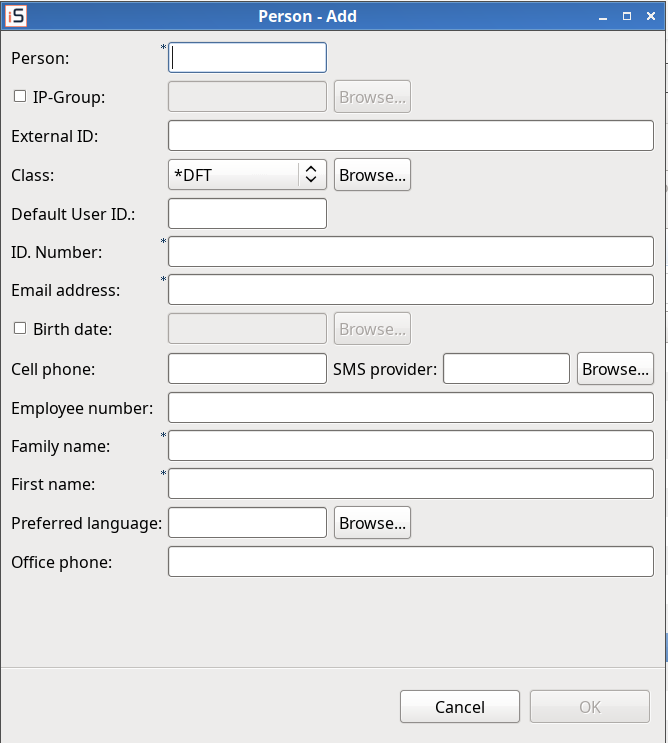
- Persons: Adjusted to native.
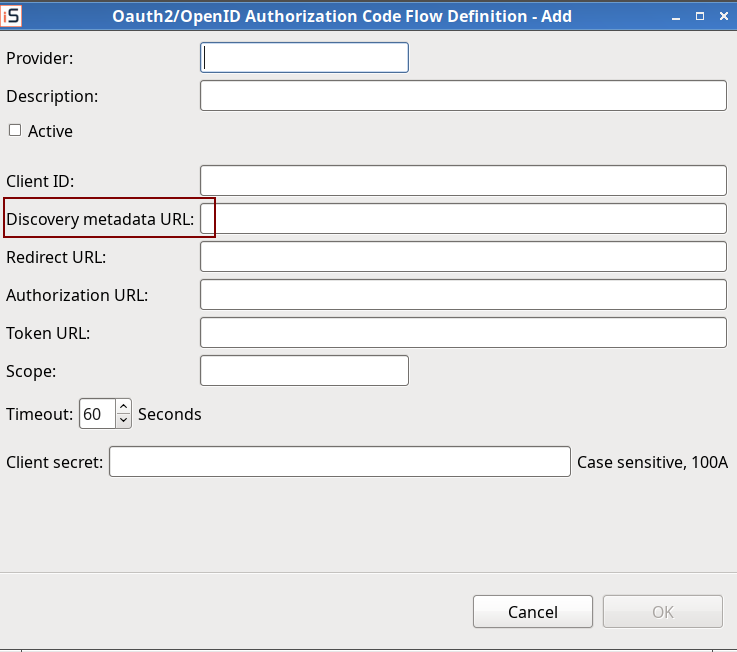
- External Authority Providers: Updated Metadata discovery URL for signature verification of JWTs in OpenID Connect and Oauth2.
Version 5.1.10 (October 2023)
- GDPR (Encryption) discovery – count records: Optimization and bug fix
- Check authorization for Capture 5250: call SMZC/GSEPWDR instead of SMZ4/GSEPWDR.
- Firewall – User/group security -Servers: if all verbs of server are allowed and server is configuring to ‘by verb’, the server is allowed too. (adjusted to native)
Dashboard
New Features
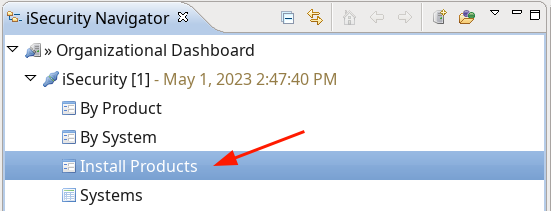
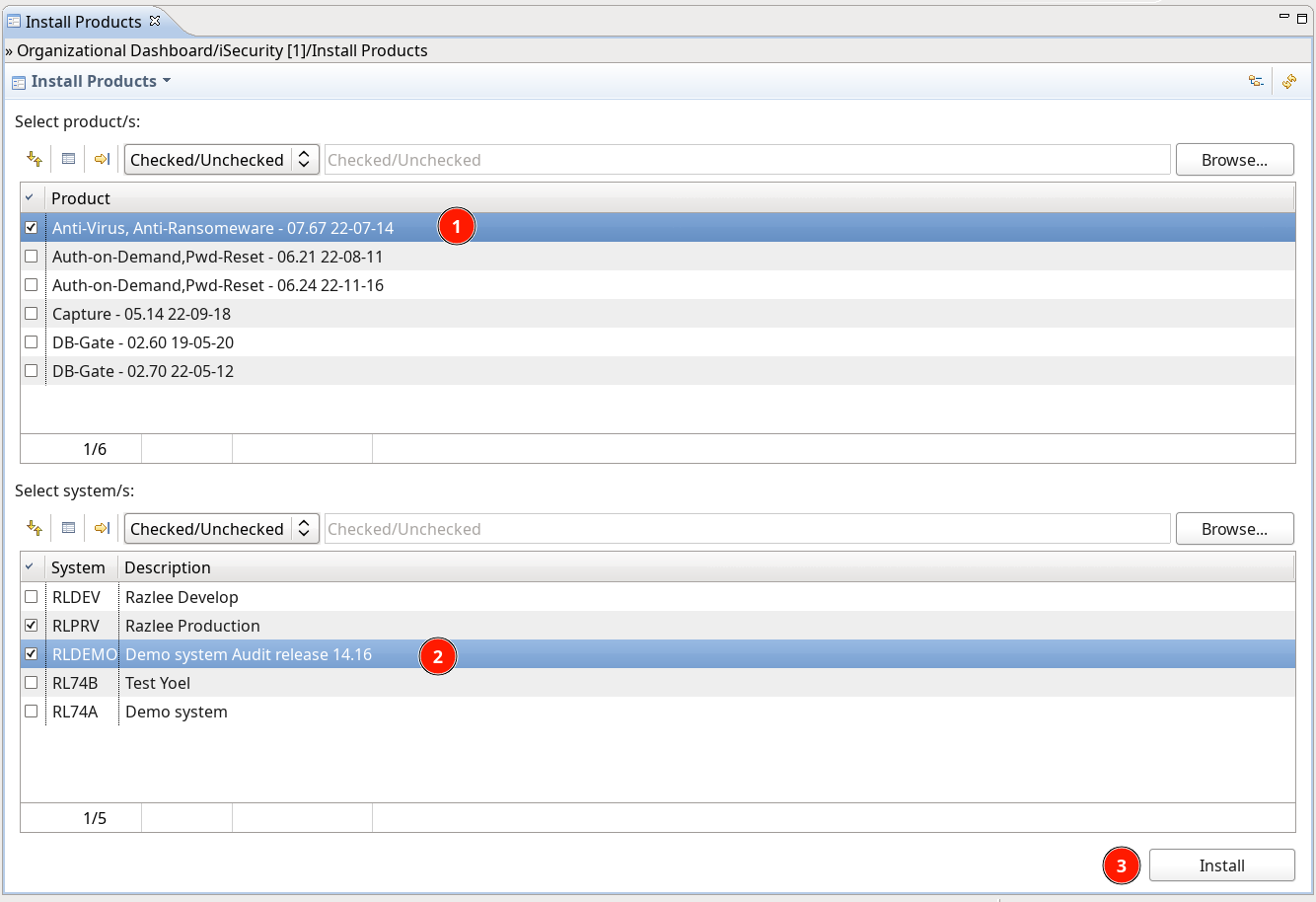
- Installation of products
Enhancements
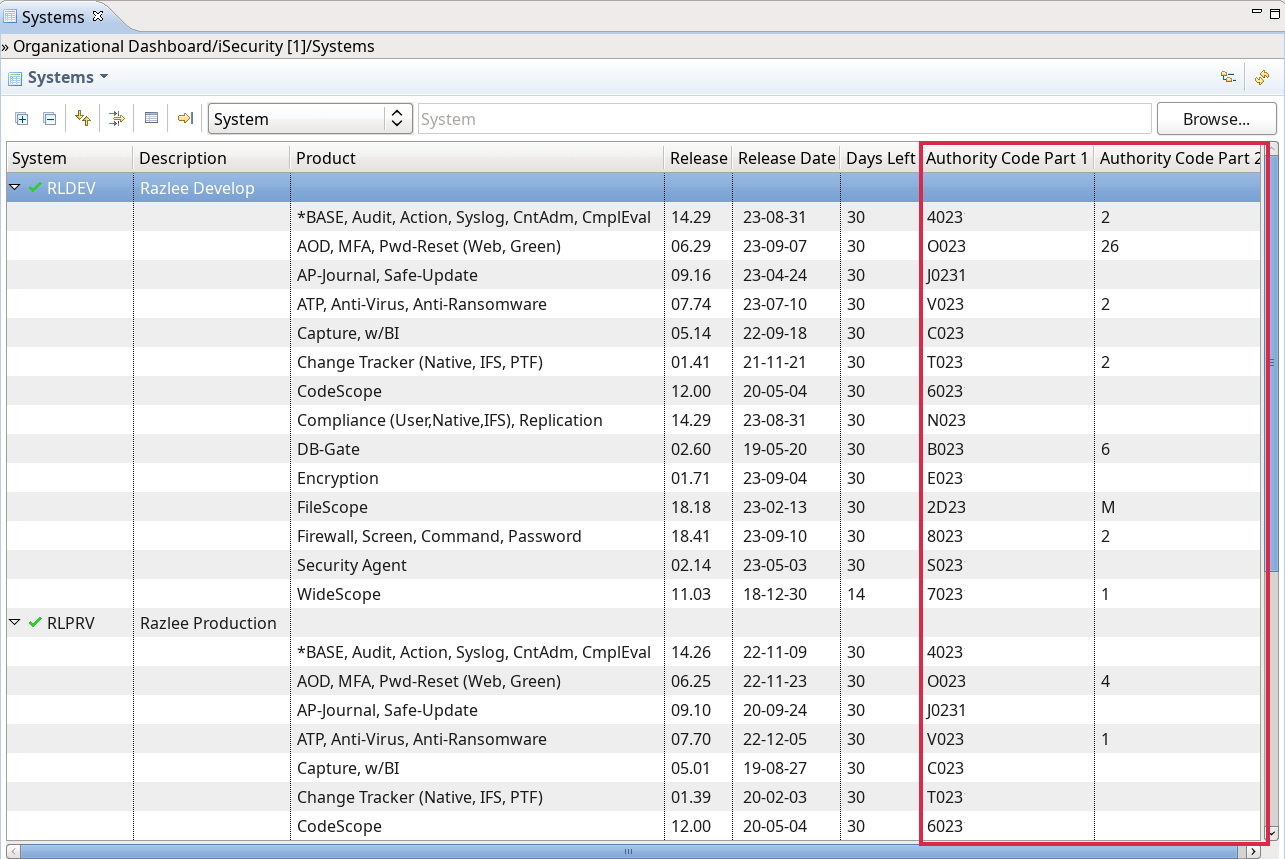
- System info: added authorization code columns
General
New Features
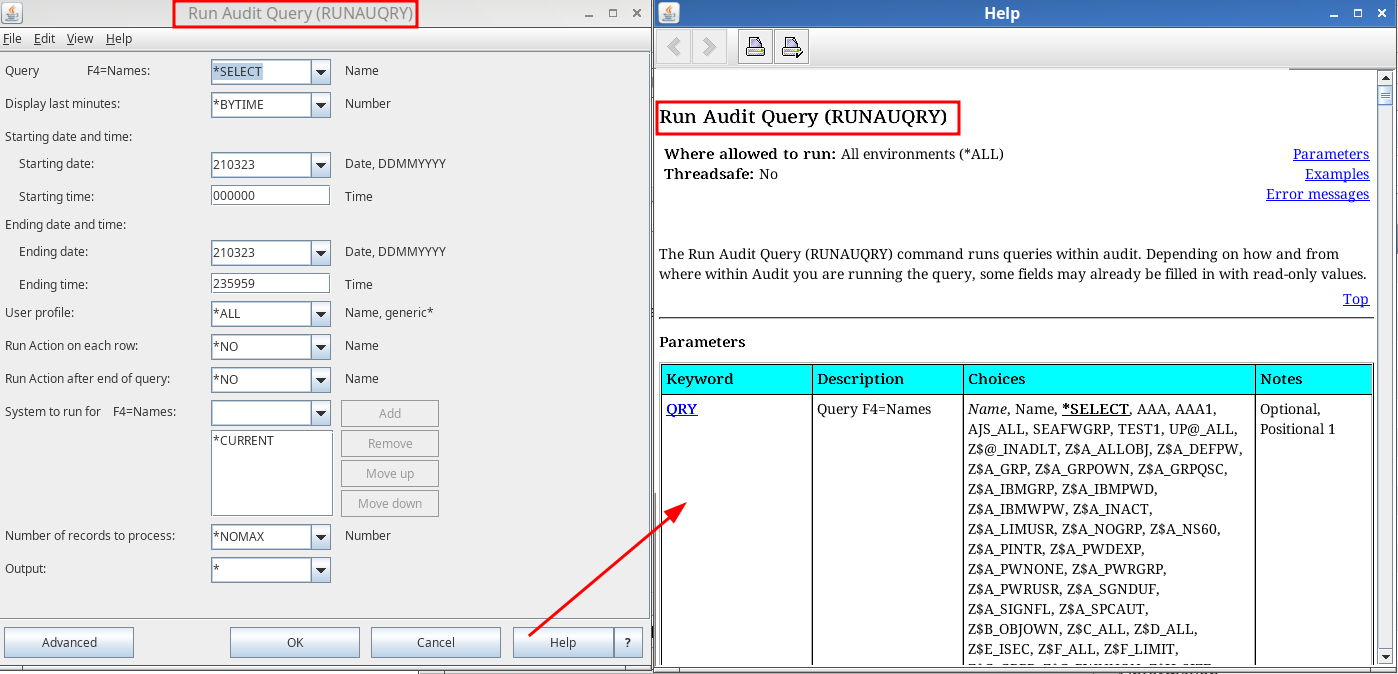
- Help is now available from the IBM’s command prompter
Audit
New Features
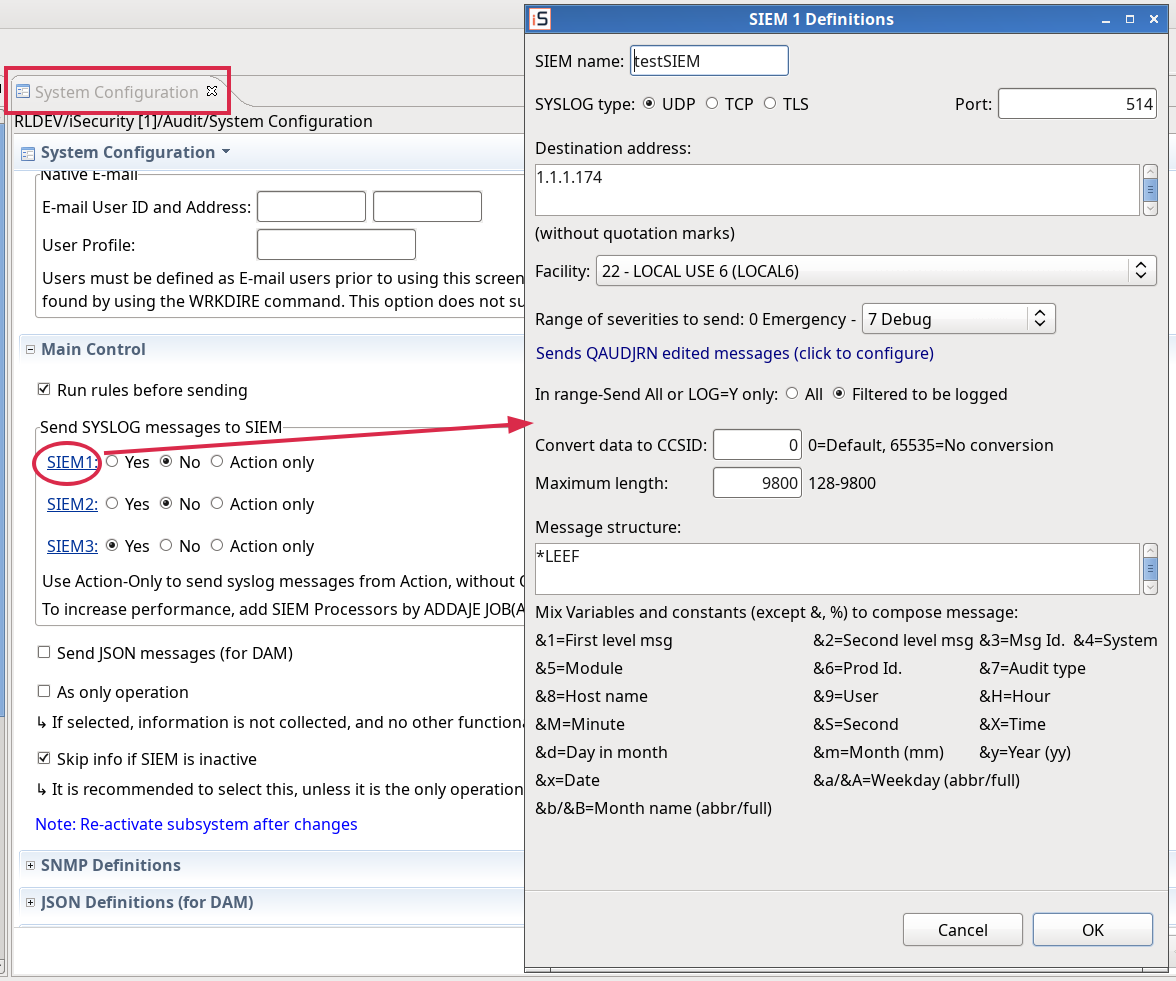
- System configuration – SIEM: adjusted to native.
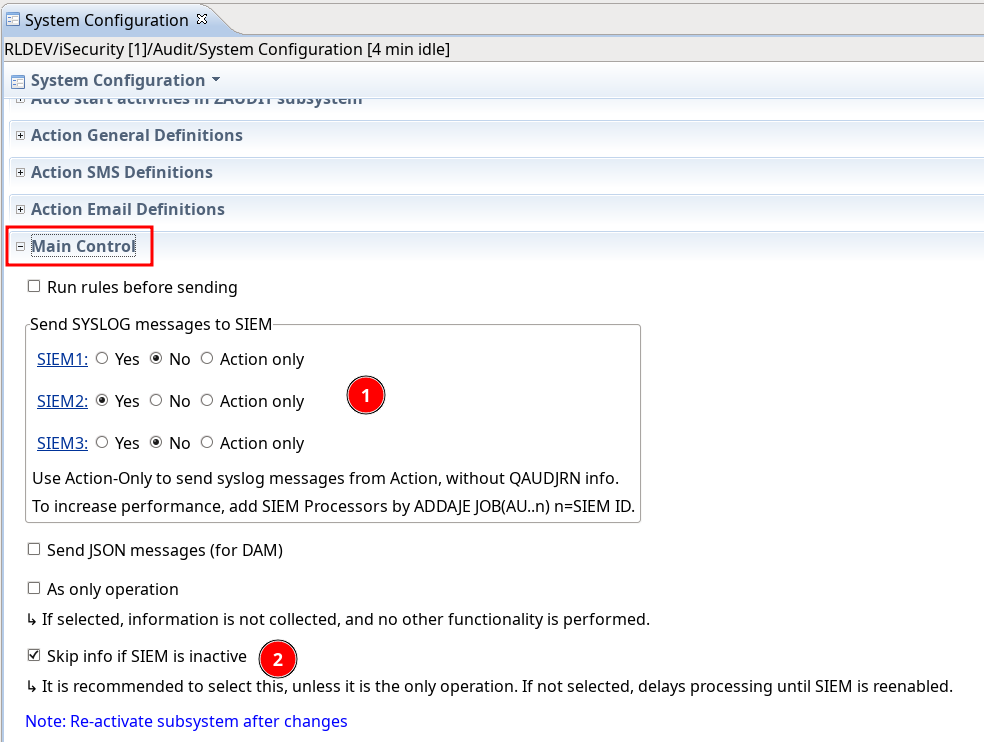
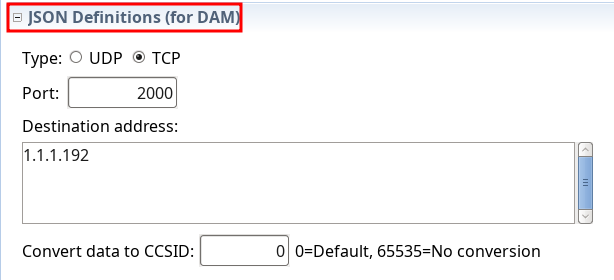
- System configuration: removed Twitter settings and added JSON Definitions (for DAM)
- QAUDJRN Severity Setting – SIEM: adjusted to native
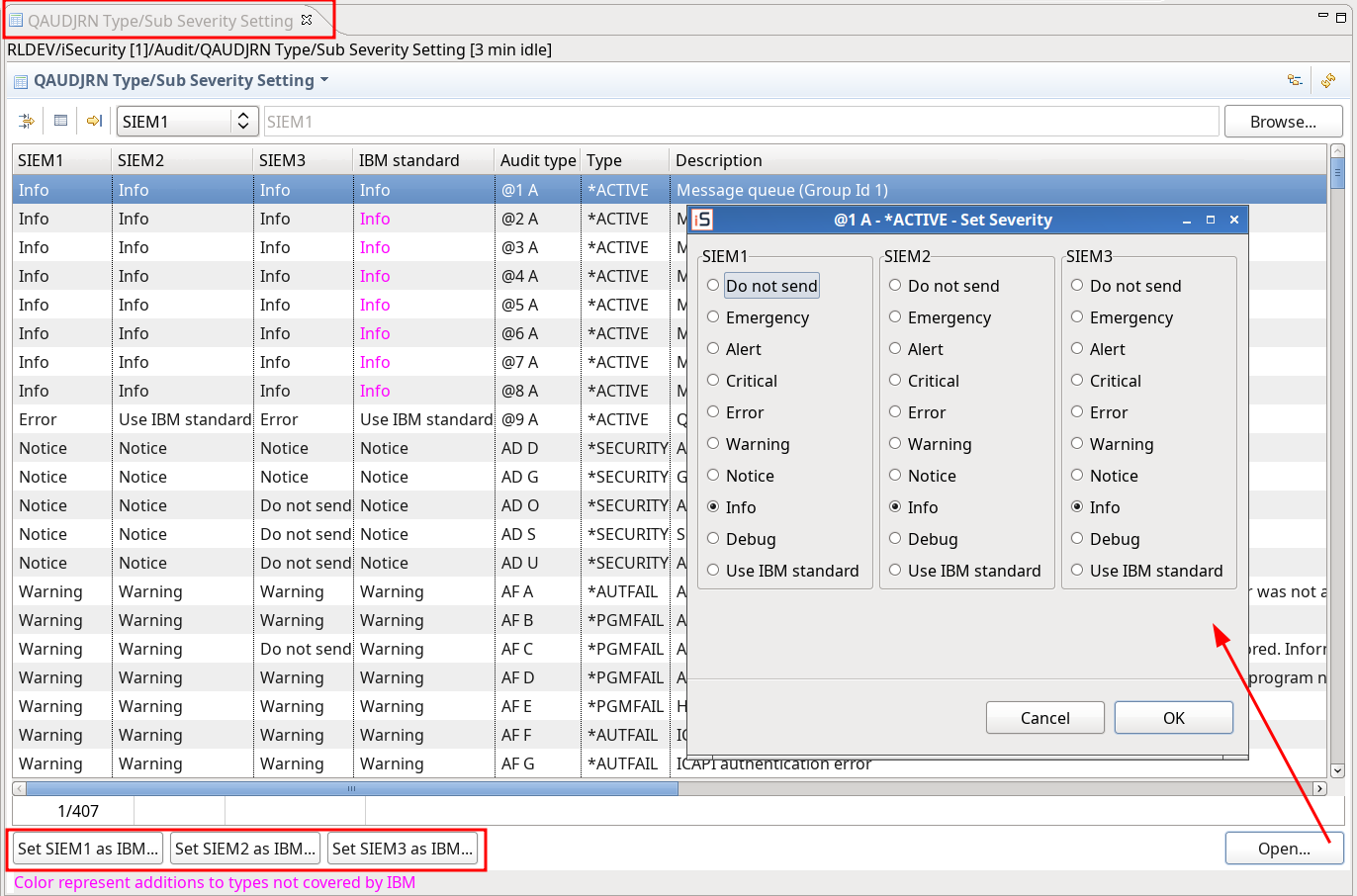
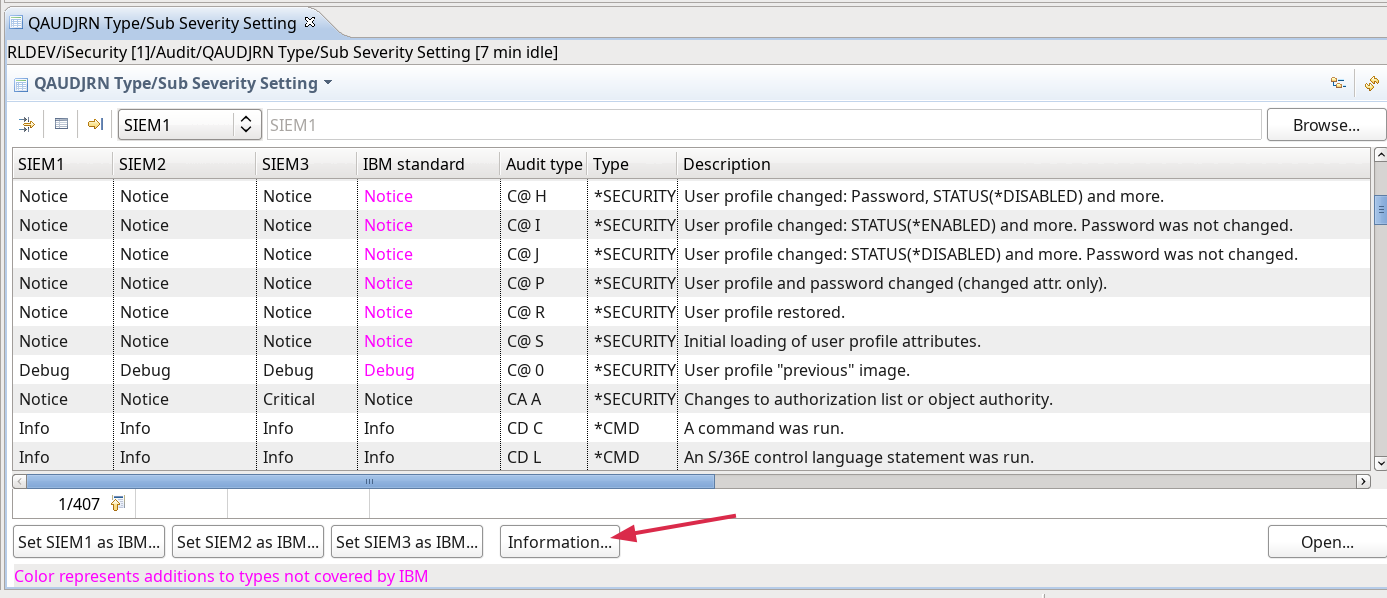
- Added QUAUDJRN info button
Firewall
Enhancements
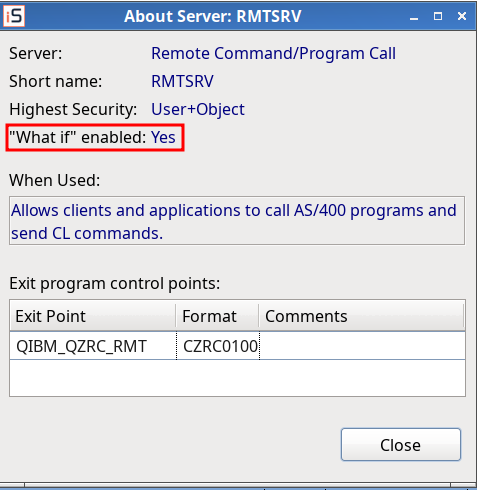
- Server Settings – About Server: added “what if” status.
MFA
New Features
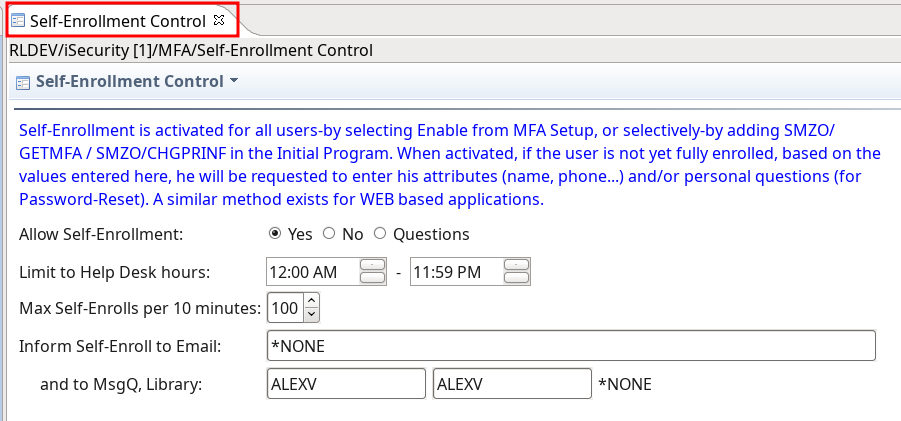
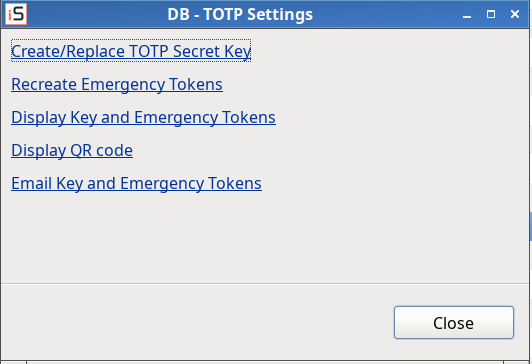
- Self-Enrollment
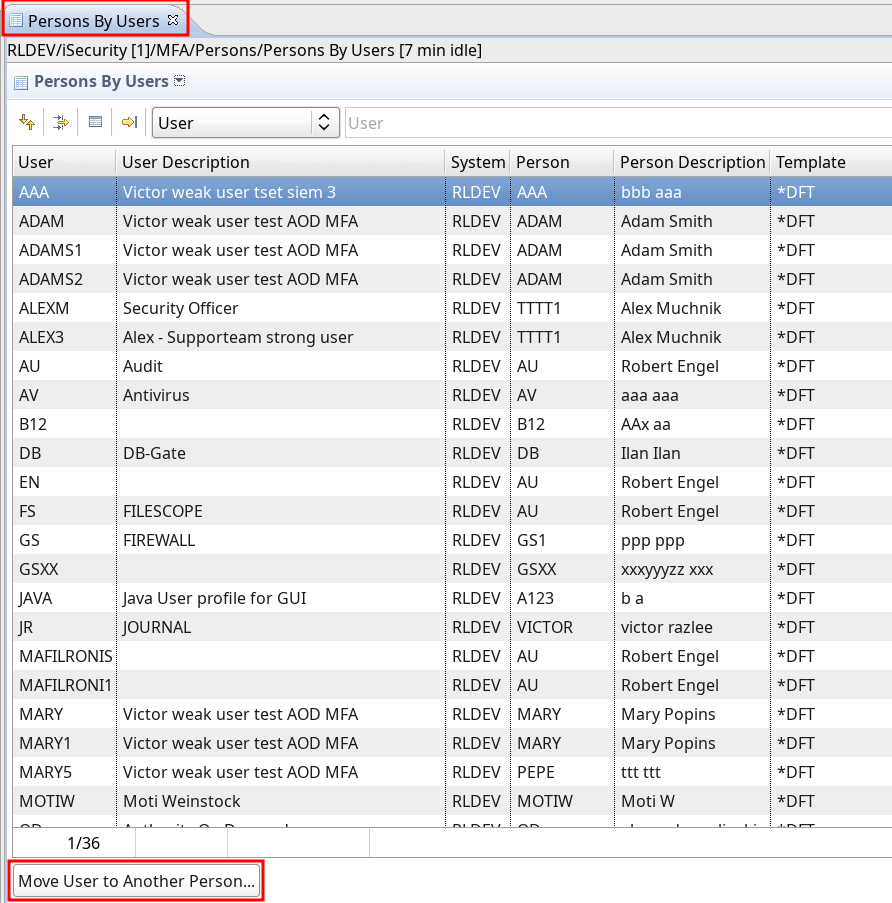
- Persons by Users
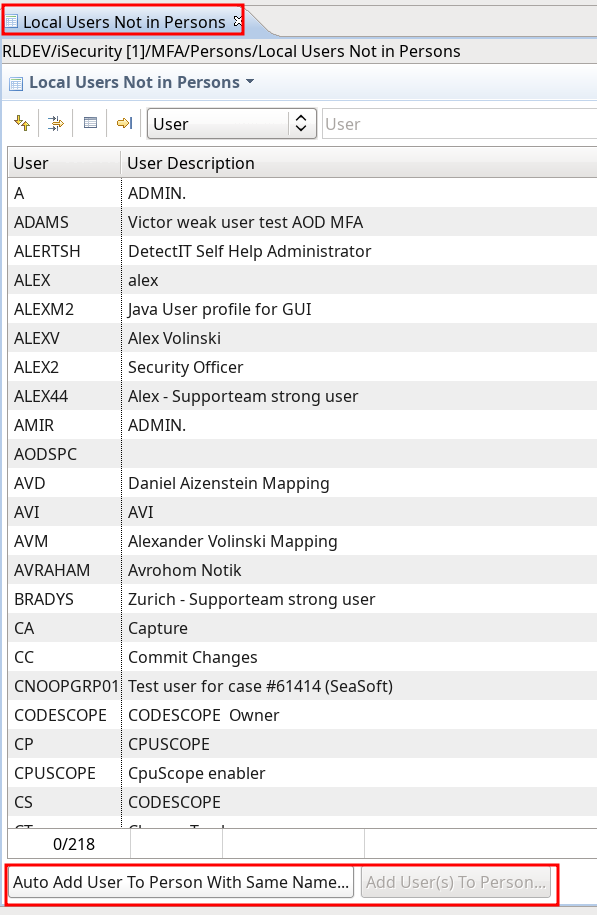
- Local users not in Person
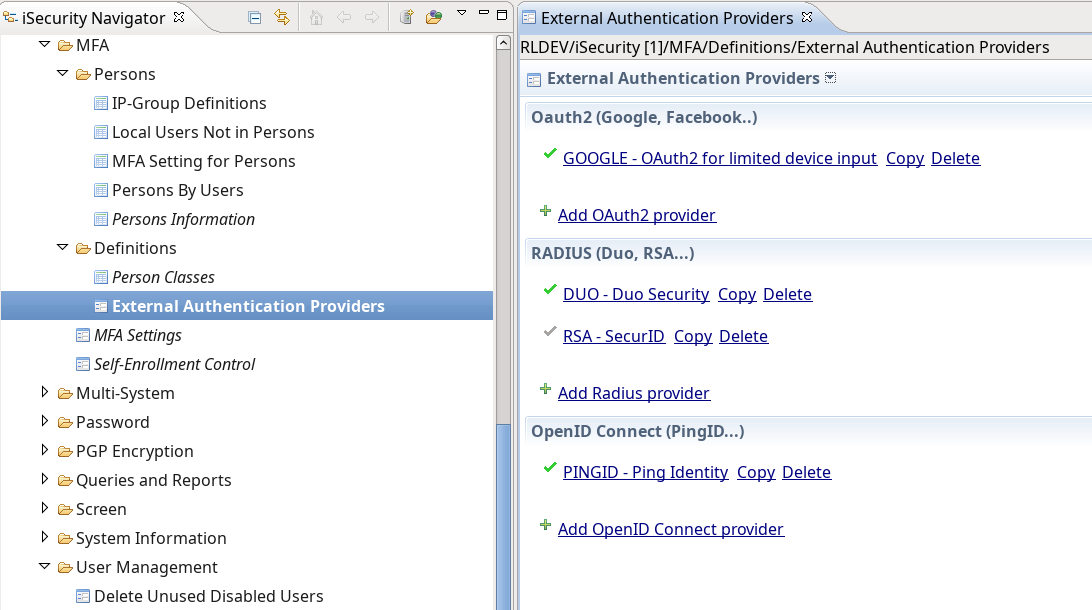
- External Authorization Providers
Enhancements
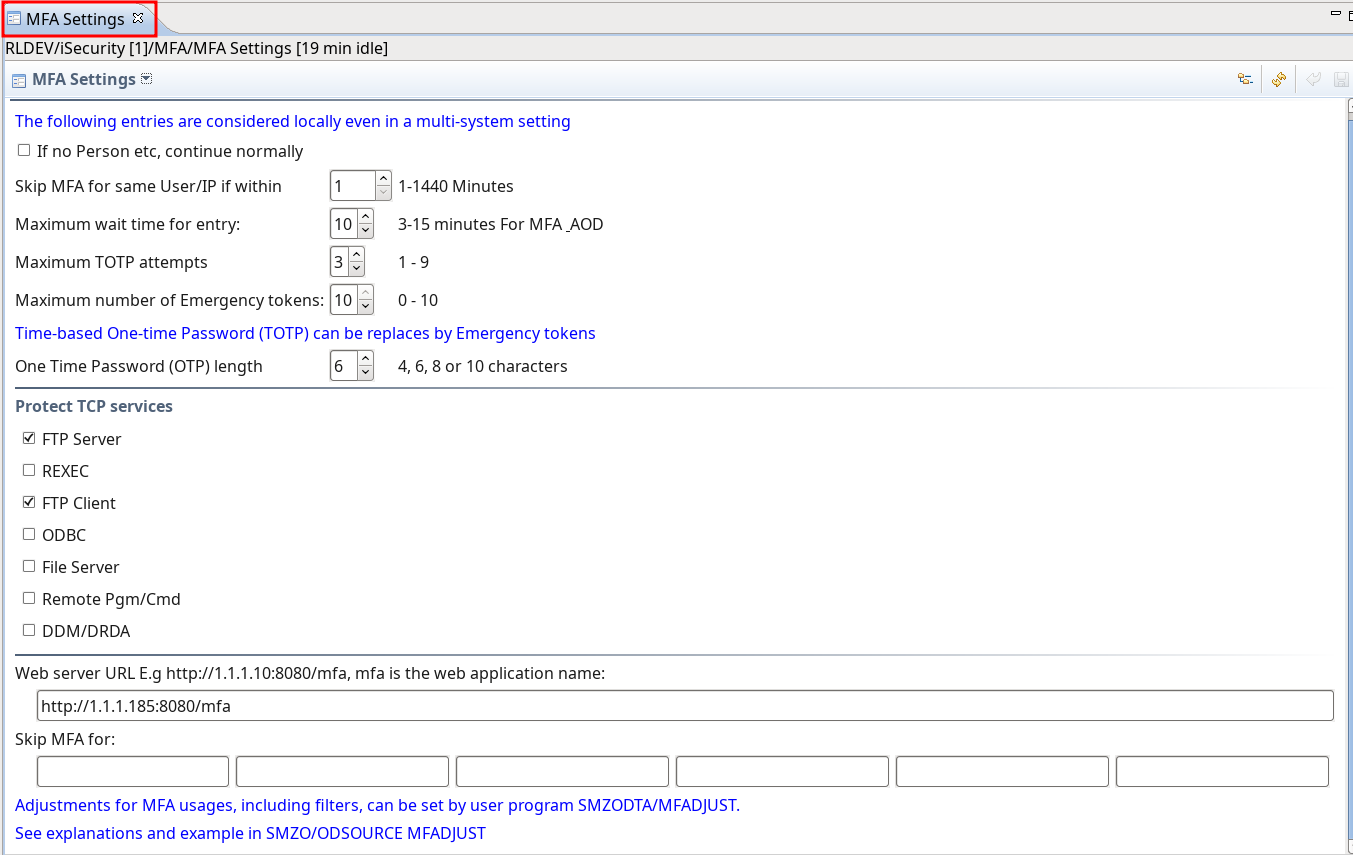
- Settings adjusted to native
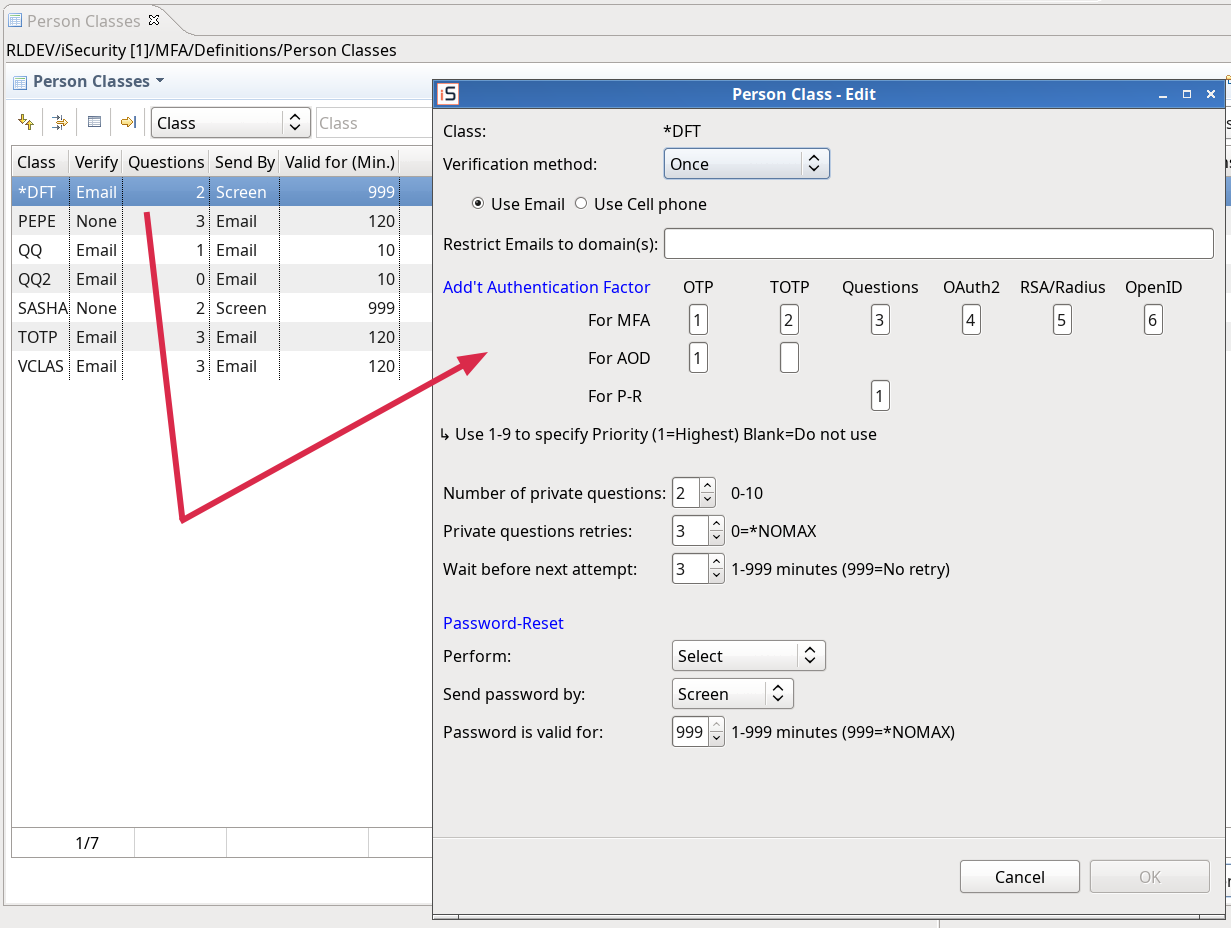
- Add/Edit PrClass Dialog – adjustment to native
Fixes
- MFA – Persons: bug fix in delete a person – the systems of the person are also deleted now
Journal
Enhancements
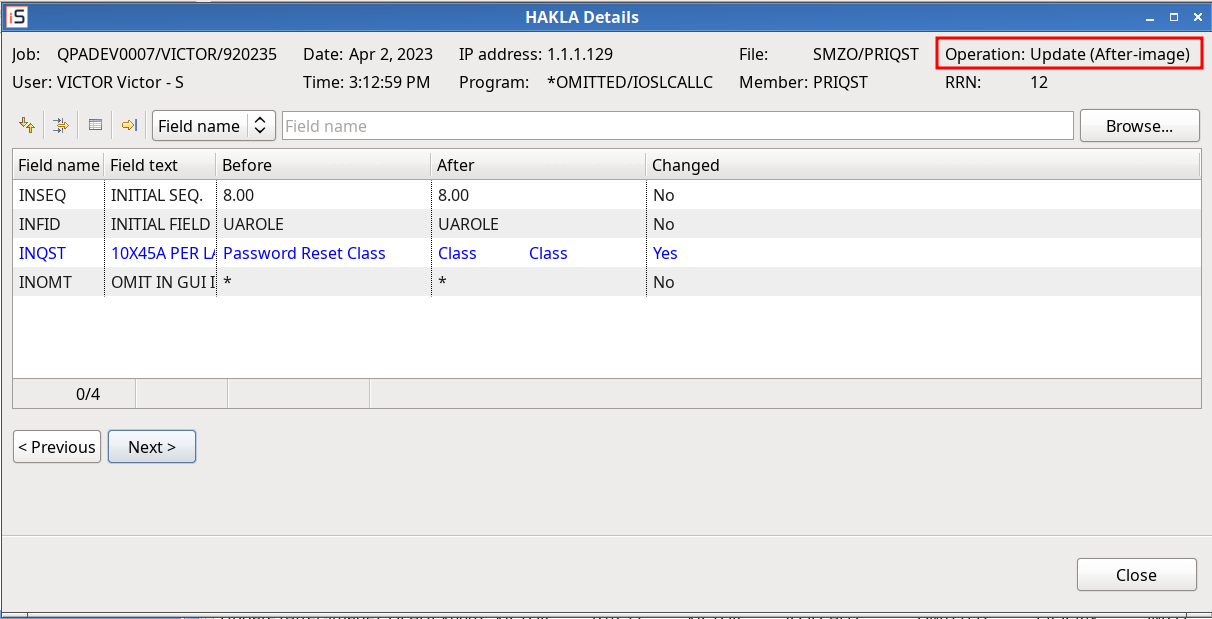
- Application Output – Operations adjusted to native
Version 5.0.90 (October 2022)
- General: Authorization program SMZ4/GSEPWDR is used now solely instead of its different copies on other libraries.
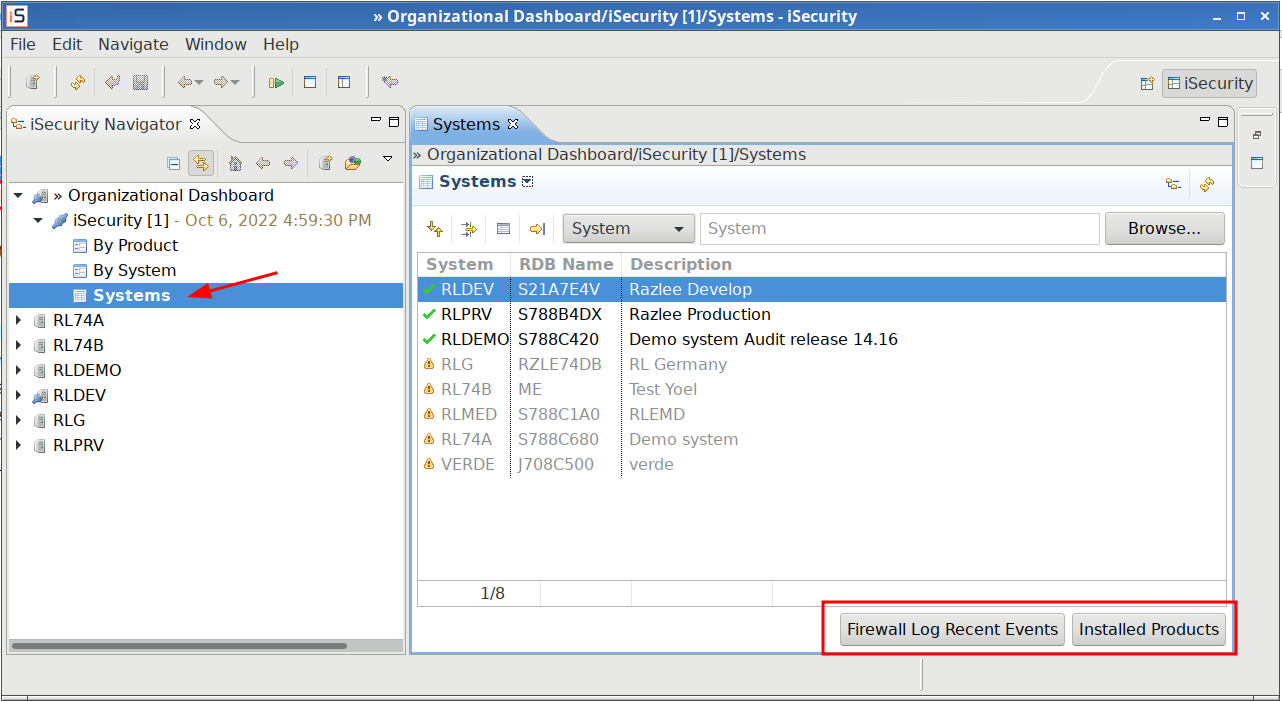
Dashboard
New Features
- Added systems table
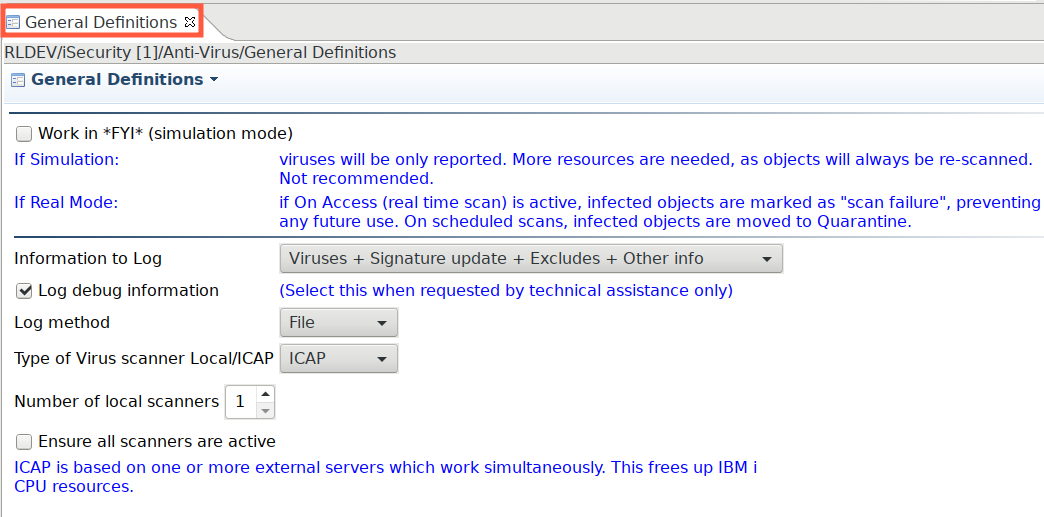
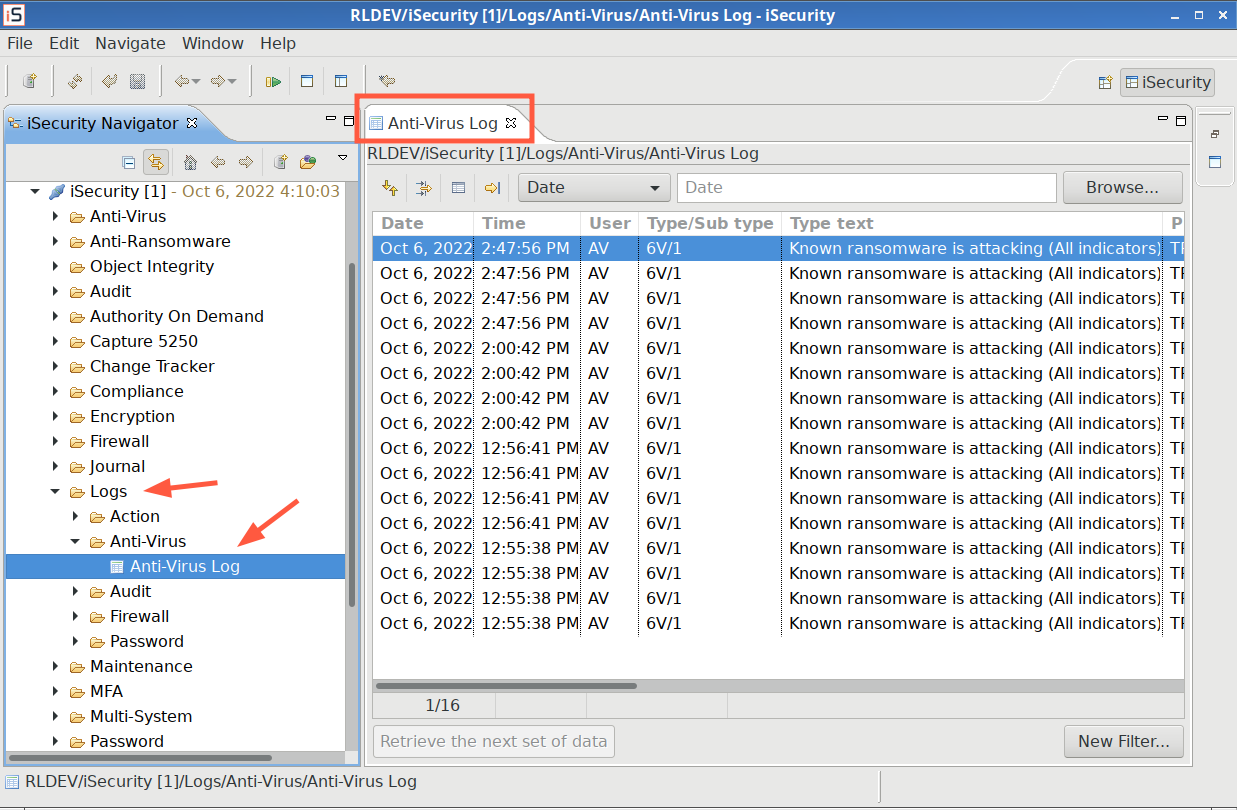
Antivirus
Enhancement
- General Definitions updated for 7.67
- Native log: AV/AR native log
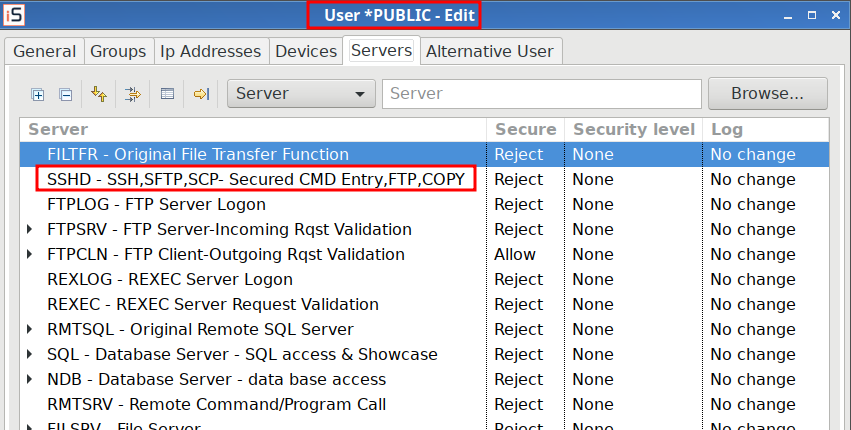
Firewall
Enhancement
- Users and Groups: SSHD settings in place of Original Data Queue Server (ORDTAQ)
MFA
New Features
- First release.
User Management
Enhancement
- Change User Profile: Added a native command that supports long user profile passwords If QPWDLVL of the system is greater than ‘1’.
